Why This Matters
Mining camps are unusual environments because they combine accommodation, logistics, welfare and workplace risk in the same footprint. A site may have hundreds of beds, rotating contractor groups, short-term visitors, transport movements, service trades and restricted plant or store areas, all turning over on roster.
Recent national data still shows mining is a relatively small but highly remote industry, and Safe Work Australia’s guidance on remote or isolated work highlights the practical difficulties that arise when people are a long way from immediate assistance, reliable communications or support networks. In that setting, camp access is not just a convenience issue.
It affects safety, incident response, key control, welfare concerns and the operator’s ability to know who was where after hours if an investigation is required. Physical keys and standalone door controllers rarely keep pace with late roster changes, emergency accommodation moves or contractor churn.
They also create a blind spot between the time access is granted and the time someone realises the wrong person still has a credential, a master key or knowledge of a restricted route. That combination of distance, contractor movement and uneven communications is why mining security decisions often sit inside broader HSE and continuity conversations rather than inside a narrow facilities budget.
If an event cannot be reviewed remotely and quickly, the cost shows up in vehicle travel, production interruption, contractor coordination and the time leadership needs to determine whether a local issue is isolated or part of a broader pattern.
How Connect Services Would Respond
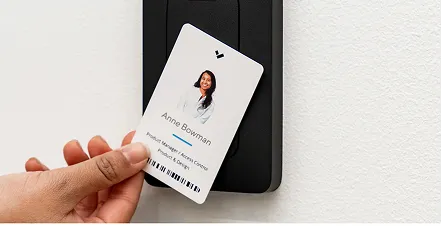
For that reason, Connect Services would usually respond with a blend of cloud-managed access control, linked credential and event management and, where the entry layout justifies it, video intercom capability for staffed and unstaffed decision points. The design would separate accommodation, administration, amenities, stores and operational zones so permissions can be issued by role, shift, contractor package or time window instead of by who happens to hold the right key.
Camp administrators would be able to activate, revoke or adjust access remotely as rosters change, while managers reviewing a night-time incident would have a clearer record of the door event, the credential used and the related footage. Within broader mining operations, that gives a remote camp a more disciplined way to manage arrivals, departures, temporary contractors and restricted zones without relying on manual key registers or fragmented spreadsheets that are already out of date by the next bus arrival.
A cloud-managed design is especially useful in mining because the same estate may include permanent plants, temporary work fronts and lightly serviced infrastructure. Standardising the operating view across those conditions helps avoid the common problem of one flagship facility getting modern visibility while exploration pads, camps or satellite assets remain trapped on older locally managed systems that are harder to govern consistently.
What This Could Improve
The benefit is stronger operational control, not a promise that every security issue vanishes. What changes is the quality and speed of decision-making.
Credentials can be removed when someone leaves site, temporary access can be limited to the right time and place, and supervisors can investigate an after-hours entry with actual evidence rather than recollection. That is especially important in camp environments where the same estate may include sleeping quarters, kitchen and wet mess areas, laundries, plant rooms, medical spaces and operational compounds, each with a different risk profile.
Better access data also supports simpler contractor management because induction status, room allocation and restricted-area permissions can be aligned more closely with the roster instead of being handled as separate processes. If the camp later expands, the same cloud-managed model can scale across new blocks or satellite compounds more easily than a patchwork of local controllers and replacement keys.
The result is a cleaner audit trail and a more defensible way to manage access in a setting where site welfare and operational accountability overlap. It also supports a stronger cross-functional response.
Operations, security, HSE and contractor management can work from the same underlying record, which makes it easier to close out actions, document lessons and show that the organisation is improving controls over time rather than simply reacting to the latest event in isolation.
Next Step
The most effective camp security projects usually begin by mapping the real access logic of the site: who needs 24-hour access, who only needs shift-based entry, which doors should stay convenient, and which ones should create a reliable record every single time they are used. Connect Services would use that practical lens to design a rollout that improves day-to-day camp administration while still supporting incident review and after-hours escalation.
That is why mining clients usually benefit from starting with a shortlist of assets where delayed awareness creates the most operational downside, then using those locations to set the standard for wider rollout across camps, compounds and remote infrastructure once the decision-making workflow has been proven.
If you are reassessing keys, restricted-area controls or contractor movements across a mining camp or village, explore the wider cloud-managed platform options and then contact Connect Services to discuss a better access model for remote accommodation and operational facilities.